G DATA Business Solutions: Configuration of the ManagementServer for remote work
G DATA Endpoint Protection Businesss offers flexible software, even for distributed remote workstations working from home.
The first question that should be clarified: how can the contact to the G DATA Management Server be realized?
In principle, security clients get the latest signature updates even without a direct connection to the G DATA Management Server (as long as this function is set correctly - G DATA Security Clients load their signatures directly from the G DATA update servers). In this case, however, the administrator does not receive any information about incidents or requests via G DATA Management Server. The clients are on the way thus "flying blind". There are also some functional limitations associated with this. For example, the G DATA Firewall would not be installable without the G DATA Management Server.
The public accessibility of the G DATA Management Server (both Main- and SecondaryServer) solves these issues.
The following scenarios are possible:
-
No contact with the G DATA Management Server possible (not recommended).
-
The G DATA Management Server is located on an internal network - it can be reached via a public IP or DynDNS and port forwarding.
-
The G DATA Management Server is located in a DMZ and can be reached directly via a public IP.
-
There is no way to make your own G DATA Management Server reachable from the outside.
There is a publicly accessible G DATA Management Server available
First, the public name or IP of the selected G DATA Management Server must be published to the G DATA clients:
Store your public IP or DNS name in the G DATA Management Server database via cmd:
sqlcmd.exe -S .\GDATA2014 -d GData_AntiVirus_MMS -Q"INSERT INTO server (Parameter, Value1) VALUES ('ServerNamesForAgents','myserver.mydomain.tld')"-
myserver.mydomain.tld corresponds to the public name or IP.
-
You can view the instance name ".\GDATA2014" as well as the database name "GDATA_Antivirus_MMS" in the configuration file on your G DATA Management Server: The file config.xml.
-
All computers that still have an active connection to your G DATA Management Server will now automatically receive the second server name as a fallback.
The following steps should then be reviewed or implemented:
-
Create a new installation package in the G DATA Administrator. (In the main menu under Organisation → Managed installation packages → +.)
For all future installations, this will contain both your internal server name and the one you have defined publicly. -
Delete all old installation packages.
-
Connections arriving at the public name or IP on port TCP/7161 must be routed to the G DATA Management Server in the next step. This can be done via port forwarding to the internal server or a second G DATA Management Server in your DMZ. Setting up a second server in the DMZ requires additional steps. Our support team will be happy to help you with this: G DATA Technical Support.
-
Computers that are already out of range will not receive the change automatically until they are back on your network or VPN. The change can also be made manually in the registry on the affected system. Execute the following command in the CMD on the affected system:
reg add "HKLM\Software\WOW6432NODE\G Data\AVKClient" /reg:32 /v SecondaryServer /t REG_SZ /d myserver.mydomain.tld /f
-
Deploy the clients according to the instructions G DATA Security Clients load their signatures directly from the G DATA update servers.
G DATA Security Clients download their signatures directly from G DATA update servers
Your G DATA Management Server is not publicly accessible and should not be in the future. In this case, the clients load the latest signatures from the G DATA update servers.
Make sure that the G DATA Security Clients receive signature updates every hour to be protected. The G DATA Security Clients will receive the latest signature updates even without a connection to the G DATA Management Server, but this will not allow them to send information about incidents or requests.
1 |
In G DATA Administrator, go to Clients → Client settings → General.
|
||
2 |
Click Signature Update Settings… on the right side of Updates. |
||
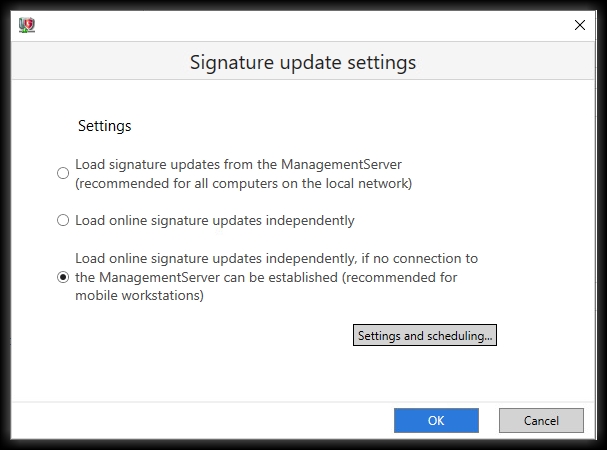
3, |
In the Signature Update settings, select the lowest option. |
||
4 |
With the option Load online signature updates by itself if no connection to ManagementServer can be established (recommended for mobile workstations), the G DATA Security Client will load signature updates by itself when it is outside the local network. However, the client communicates with the ManagementServer as soon as it is on the local network, without making any changes to the settings.
|
||
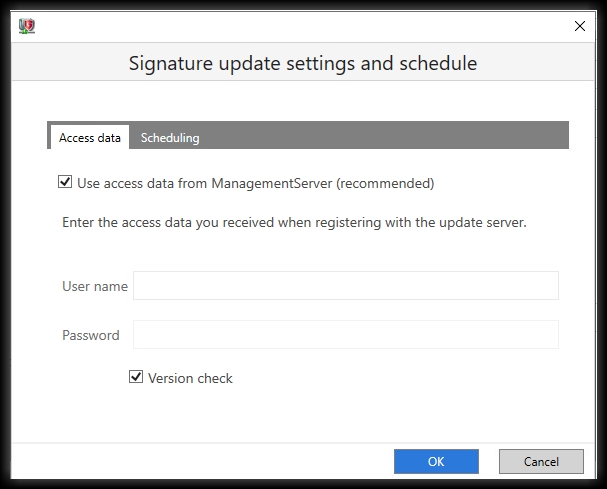
5 |
Click on Settings and Scheduling. |
||
6 |
Activate the option Use access data from ManagementServer, or enter the access data. Activate the Version check. Version checking only loads signatures that have changed since the last update. Without version checking, the complete virus
signatures are always loaded.
|
||
7 |
Click Schedule at the top of the window. |
||
8 |
Select Hourly to get the optimal protection. |
||
9 |
Click OK to save the signature update settings and schedule and close the window. |
||
10 |
Click OK to save the signature update settings and close the window. |
||
11 |
Click Apply at the bottom right to save your changes. |
No publicly accessible G DATA Management Server is available
For computers working remotely from home but connect to your company’s network on a regular basis (laptops), it is sufficient to set them up according to the instructions G DATA Security Clients load their signatures directly from the G DATA update servers.
However, if you never come into the company network, there are various ways to protect your home workstations. Here, the decision is whether to hand over responsibility to the individual user (for example, through a G DATA Desktop solution) or whether the administrator should retain responsibility and control here as well. Many of our partners offer client management via public G DATA Management Servers. Our product "G DATA 365 | Managed EDR" would also be such an alternative.
We will find the right solution for you! (→ Contact form).