Additional data security with G DATA ID Protection
What is G DATA ID Protection?
With G DATA ID Protection you reliably protect yourself and your data against identity theft and other forms of cybercrime. The application compares your data with known data leaks (hereinafter "leaks") and can thus protect them in real time by informing you when new leaks are found and enabling you to take immediate action. This is an add-on product and can be purchased if you already have a G DATA home security solution via My G DATA, or in combination with one of our G DATA products for home users in our shop.
| If you are still unfamiliar with the My G DATA portal, you will find here all relevant Information. |
In addition to detecting whether an email address you use has been compromised, G DATA ID Protection also protects and monitors the following important data points and accounts:
-
Five E-mail addresses
-
Five Bank details
-
Five credit card numbers
-
Five telephone numbers
-
A driving licence number
-
Two PayPal accounts
-
Up to 15 social media accounts
| Supported social media accounts are: Adobe, Amazon, Facebook, Flickr, Gamertag, Google, ICQ, Instagram, Linkedin, Skype, Steam, Telegram, Tumblr, Twitter and YouTube. |
How do I navigate to the user interface of my G DATA ID Protection?
After purchasing the add-on product G DATA ID Protection, you can access the user interface of the application directly or access it through the application via the My G DATA portal.
If you choose the direct way, you will get to the login screen of G DATA ID Protection.
| The access data required here are the same as for your other G DATA Consumer Products, which you also use for the log-in at the My G DATA portal. |
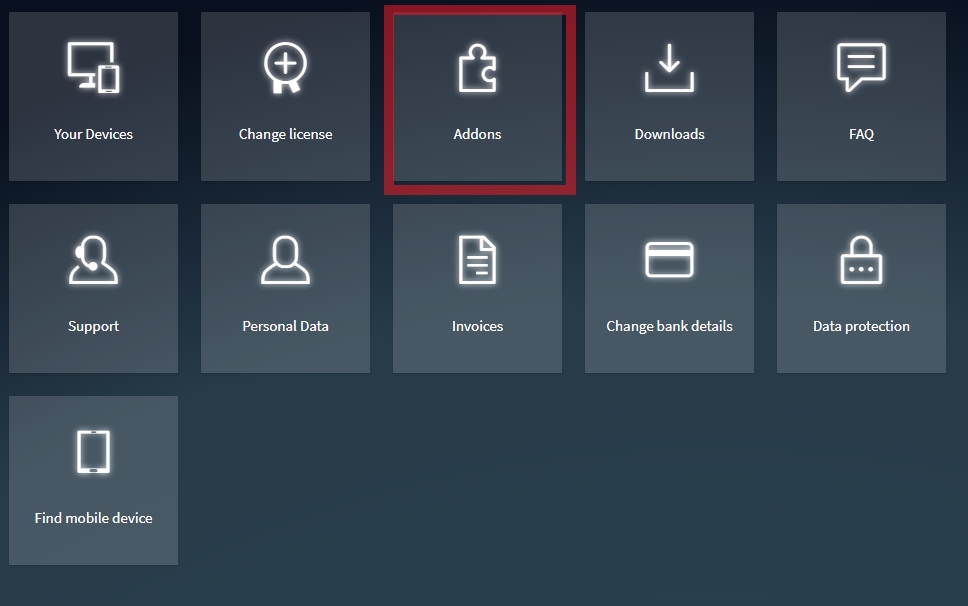
If you want to reach G DATA ID Protection via My G DATA, click onto Addons after logging in.
Show Screenshot
In the window that then opens, select "ID Protection" at the top and then click on Open app.
Show Screenshot
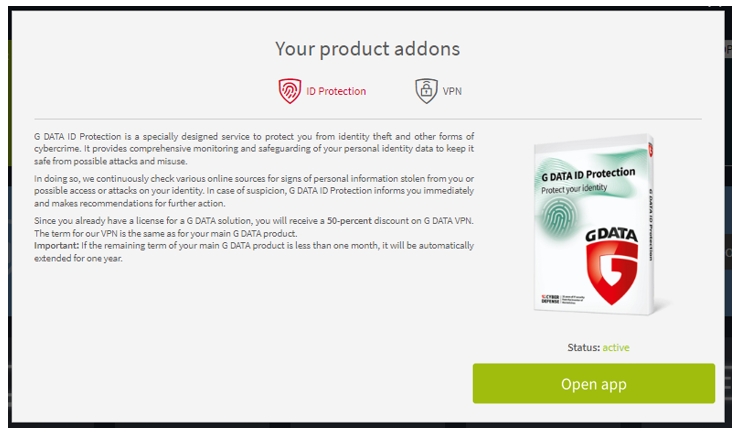
You will be redirected to the G DATA ID Protection user interface and automatically logged in.
User interface of G DATA ID Protection
The user interface of G DATA ID Protection consists of two main areas, a view of all your data and accounts to be protected and an overview of all leaks that have been discovered.
What happens when leaks are discovered?
If a leak is discovered in relation to the data you have entered, you will first be notified by e-mail. This e-mail will be sent to the address you used to register with My G DATA. The information on all leaks concerning you will be collected and processed at G DATA ID Protection.
All leaks are displayed under "My data" in the relevant section as shown in the screenshot below.
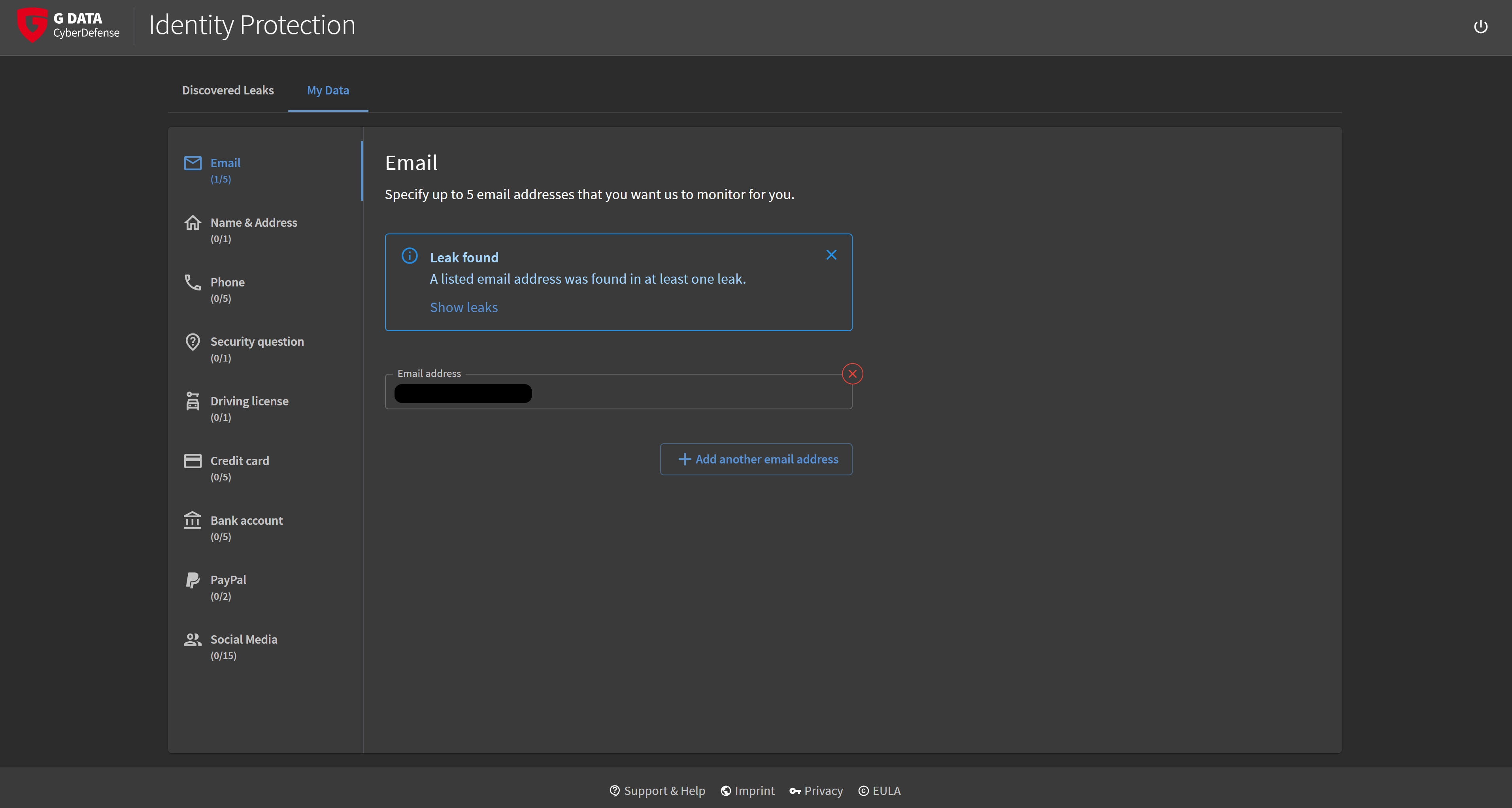
In addition, all leaks are collected in the "Discovered Leaks" view. Here you will find detailed information as well as instructions how you can best deal with the respective leak.
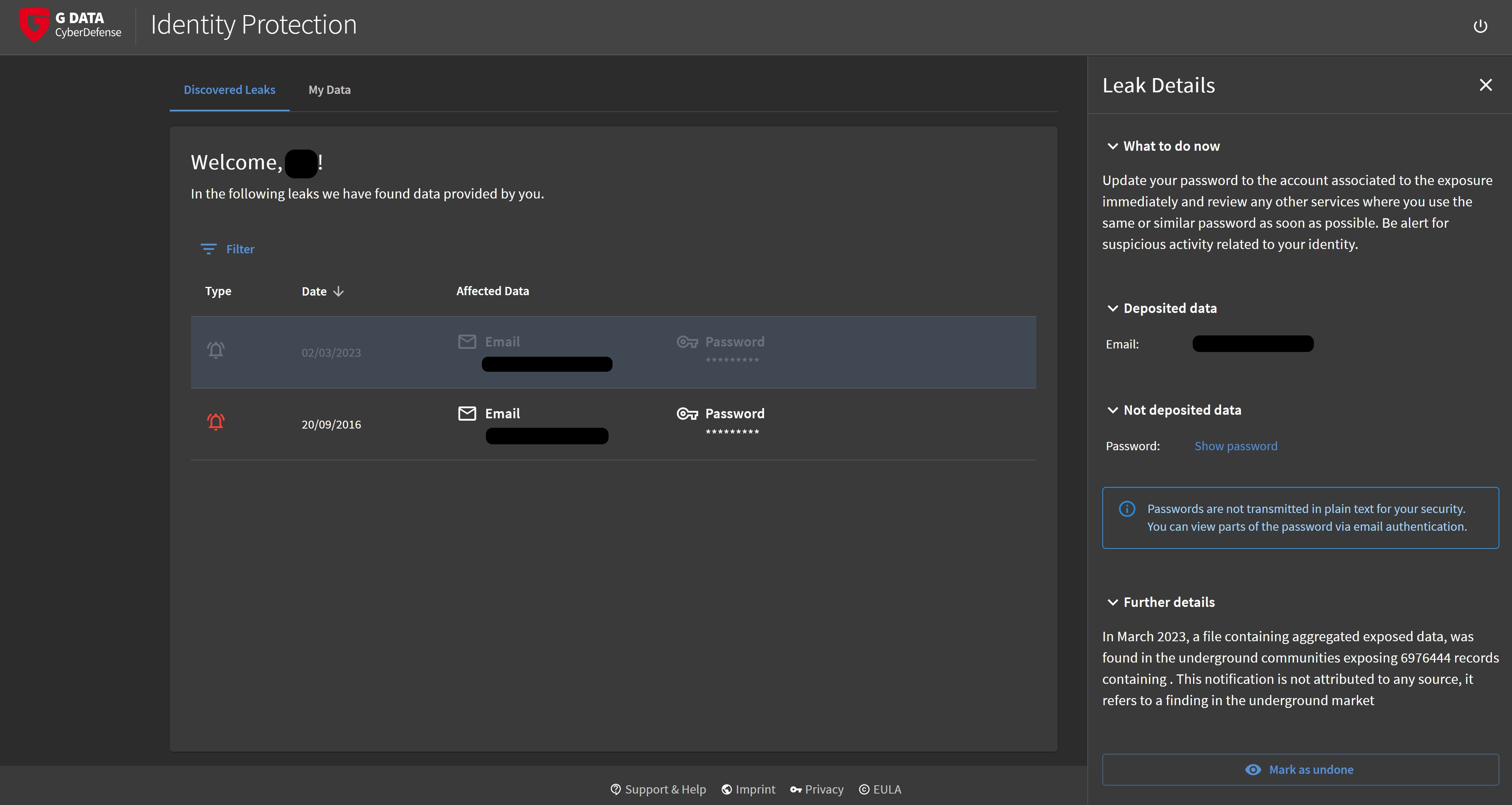
After carrying out the instructions for action and rectifying the problem, the corresponding leak can be marked as resolved.
| Even after individual leaks have been marked as resolved, they are still displayed greyed out in the "Discovered Leaks" view. This means that no important information is lost and no harm is done if a leak has been mistakenly marked as resolved. |

